Today’s post is highlighting those horrible Indian Call Centres that run Microsoft Support Scams to prey on the old and the not so tech-savy people who have computers>
I received a request from a friends Auntie, who despite her advancing years has a computer and regularly uses it for the internet and keeping in touch with far flung family via email and Skype, unfortunately she’d had a call from a company called WindowsPCSupport who said they were Microsoft Support and a problem had been found on her PC that was being reported back to them.
I’m sure you can guess the rest :
She was fooled into installing and allowing them access to her PC, where upon they opened various report logs on her PC that showed error messages and convinced her that her PC was infected with a virus.
They then told her it would cost X amount of money to fix it and then proceeded to take her Credit Card details.
They then spent the next 2 days harassing her via the phone as the payment had not yet gone through, they also proceeded to lock her PC with a SAM hive encryption Password, so she was unable to access her PC at all unless she provided them with a payment.
It was at this point I got involved:
First thing I needed to do was ensure that she cancelled the payment with her Credit Card company and at the same time request a new card, as the Scam company now had her CC details and there was always the possibility that they could either sell them on or use them to buy goods for themselves with her money.
Next thing to do was to get the PC unlocked so she could access it
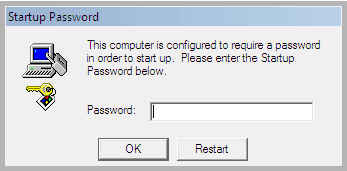
After getting the PC home and connected the first thing we see on the screen is the following
The Windows 7 icon appears and then a box shows up saying “this computer is configured to require a password in order to start up”
Now normally when PC’s are locked with Passwords you can generally use a Password Reset Utility on something like ERD Commander or a Hiren Bootdisk which allows you to get into the computer and run the Reset Utility, but unfortunately this doesn’t work with SAM Hive Encryption.
So what do you do then:
First thing get hold of a bootable disk like ERD Commander or WindowPE
Place the Bootable Disk into your CD drive and reboot your PC
As the PC Boots up you’ll see an option for “Boot Options/Boot Order” usually its F8 or F12
Press the relavent F Key when it asks and this will take you to the PC’s Boot Menu
Choose to Boot your system from the CD Drive
The ERD Commander or WindowPE disc will then begin to boot your PC, at some point it will ask you to choose a partition to boot from, do not choose your Windows Partition, use the Bootable disks own.
This should then boot you to ERD/WindowPE Desktop, now its just a case of opening the Computer Icon on the Desktop and opening the listed C;\ Drive and navigating to the following folder
Windows\system32\config
Now locate the following Registry Hives contained within the \config folder and copy/move them to a new folder on the C Drive call it something easy to remember like “ConfigBackup”
The Registry Hives you need to copy are :
SOFTWARE
SYSTEM
SAM
SECURITY
DEFAULT
Once you’ve done this now navigate to the folder Windows\system32\config\RegBack .
In here you will find earlier copies of the registry Hives that were hopefully created before the scammers got access to your PC.
Now copy the same Registry Hives from this folder (the same files as listed above) into the Windows\system32\config folder.
Now Reboot the PC.
Now if its all worked your PC should now boot into Windows 7 🙂
Finally run Malwarebytes or SuperAntiSpyware software on your PC to ensure there are no nasty surprises been left behind by the scammers.
I shall shortly be returning the PC to my friends Auntie and no doubt receive her gratitude for a job well done.
If you’ve found this post helpful please feel free to comment and share 🙂
If you need help with this or any other IT Issues, feel free to leave a comment and I’ll see if I can help or at least point you in the right direction.